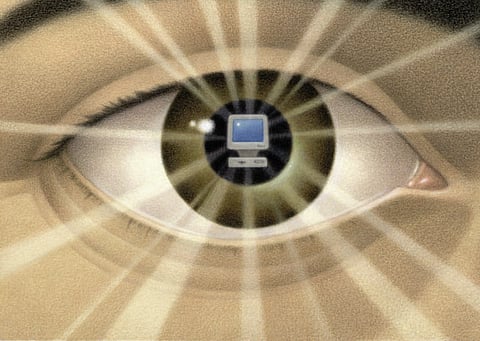
Who’s watching you?
Privacy falls by the wayside as the digital and physical worlds converge, and most of the UAE’s 1.5 million victims of cybercrime have only themselves to blame
The ongoing US National Security Agency (NSA) Prism leaks reveals one simple fact: with enough computing power and a bunch of smart algorithms, you can snoop on entire nations and populace. In just one month — March — the NSA collected 97 billion pieces of intelligence information from computer networks worldwide. Iran topped the list with 14 billion, followed by Pakistan (13.5 billion), Jordan (12.7 billion), Egypt (7.6 billion) and India (6.3 billion).
Privacy appears to be a myth, especially on the internet. Almost everything you do can be tracked, analysed, correlated, profiled. If it’s digital, it’s a data point. Your data, and data about you, is the new gold mine for governments, advertisers and hackers.
James Lyne, Director of Technology Strategy at Sophos says never before have the digital and physical worlds been as interlinked as they are today, with social media, GPS, widespread data sharing and all kinds of apps. “It’s incredible how much information a casual, let alone targeted, attacker can extract about a person,” he says.
While people are making their own minds up about government surveillance, but most don’t want employers spying on them, let alone hackers. US student Mandi Grandjean says she’s fine with the government doing secret surveillance of phone call records and internet exchanges — including on social networks — to combat terrorism, but believes it’s different when it comes to an employer or other body.
“I am personally not a fan of big government,” she told AP, “but I understand there are needs for security.”
Just as there is an app for everything, there seems to be a hack, too. Lyne recently demonstrated some malicious code that was on sale for $500. “It provided comprehensive surveillance capabilities and had been tested to make it extremely elusive. It’s all very creative and unfortunately there’s a great deal of it out there,” he says.
A staggering amount of malware, spyware, Trojans, worms and malicious scripts is being churned out, with the explicit goal of destroying your privacy or crippling your devices. “At SophosLabs we now see in excess of a quarter of a million individual new pieces of malicious code every day,” Lyne says. And the major means of distribution of this malicious code is from legitimate websites that have been hacked. “We see more than 30,000 of these every day. There have been a number of high-profile infections in the Middle East.”
There is an endless barrage of threats out there. We look at some of the most common.
Phishing for your identity
V. Balasubramaniun, Marketing Manager — IT Security Solutions at asset management software firm ManageEngine, notes that with nearly 40 per cent of people in the Middle East having internet access, a large number — in the UAE in particular — are using social media sites. “Its sheer popularity attracts the attention of cybercriminals looking for ways to harvest online identities.”
He believes that, despite untiring awareness campaigns by social media giants, even tech-savvy users are falling prey to attacks.
Adds Tamim Taufiq, Head of Consumer Sales — Middle East and North Africa for computer security software corporation Symantec, “As the frequency of visits to social networks increases, so does the threat. People, without verifying the source, start sharing info, while someone in the back end steals their identity.”
Sean Newman, Field Product Manager — Europe, the Middle East and Africa for network security hardware and software developer Sourcefire, believes today’s attackers are not in it for fame and glory but for political or financial gain. “Indeed, these well-resourced criminal gangs would rather conduct their activities quietly without you realising it than make noise. The days are over of a triumphant message appearing on your screen saying, ‘You’ve been owned.’”
World leader
The UAE has the dubious distinction of being above global averages. According to the NCR, 55 per cent of online adults experienced cybercrime last year, as opposed to 46 per cent for the rest of the world.
Taufiq attributes this partly to the trend in the Middle East of users replacing devices faster than ever before, passing on older ones without properly erasing them. “The chance of those devices ending up in the wrong hands is something of a phenomenon here,” he adds.
Lyne brings up another issue — consumerised smartphone adoption is relatively high in the Middle East, with employees using their own devices commonly. “This can be a challenge, as it makes it hard for IT security staff at businesses to ensure the devices are protected, potentially leaving users more exposed than elsewhere,” he says.
Master key
Balasubramaniun explains that with so many online tools and services, it becomes an uphill task to remember different passwords — so users take the easy route of using the same password everywhere. “This single master key practice makes hackers doubly happy. Their job gets greatly simplified. Through a simple phishing email — communications appearing to be from social web sites are commonly used to lure the unsuspecting public — hackers could easily harvest the username and password of your social media account.”
Then the domino effect rolls in. Soon your entire online life could be in danger.
Neither does it help that passwords are often easy to guess. As Taufiq muses, they are often “your daughter’s name or birthdate”. Getting those is as easy as logging onto Facebook.
Proper password management really needs to become a way of life, adds Balasubramaniun.
Pay up, or else
Public hotspots are expected to grow to nearly six million by 2015. Taufiq warns against shopping or banking on these. “Anything you share is open to snooping by anyone,” he notes.
Adds Lyne, “You may also want to keep an eye out for rogue wireless networks, a trend that is rife in cities such as London, but also Dubai.”
And the winner is…
Privacy breaches through spam messages are common. The 2012 NCR report says 31 percent of users received a text message from someone they did not know, asking them to click on an embedded link or dial an unknown number.
Finally, an important privacy threat is your own overconfidence. As NCR notes, “Three out of 10 do not think about cybercrime when online because they do not expect that it will happen to them.”



