Mobile threat: Hack attack
Your sensitive information, bank details, secret dealings... all risk being compromised
Dubai: Janice Andrade is furiously tweeting, BBMing friends, updating her Facebook status and sending out laugh out loud (LoL) jokes on WhatsApp…
The young sales executive is, however, not the only one engrossed in her shiny smartphone.
Oblivious to Andrade, thousands of cybercrooks around the world are equally interested in her phone, trying to breach her privacy and steal sensitive information.
Welcome to the ugly world of mobile hacking.
Hackers are increasingly turning their attention to smartphones today. Unlike computers, hacking smartphones is easier as hardly any of them have anti-virus or anti-spyware security.
"Bad guys go where the money is," said Charlie Miller, principal research consultant with US security firm Accuvant Inc. "As more people use phones and keep data on phones, and PCs aren't as relevant, the bad guys are going to follow that."
To get a perspective of the problem, one has to just look at the realms of personal information stored on smartphones - call history, contacts, messages, social networking and other apps, banking details, credit card details, browsing history and patterns, digital signatures - virtually everything written in tech code.
Imagine what could happen if all that stuff falls into the hands of cyber-criminals?
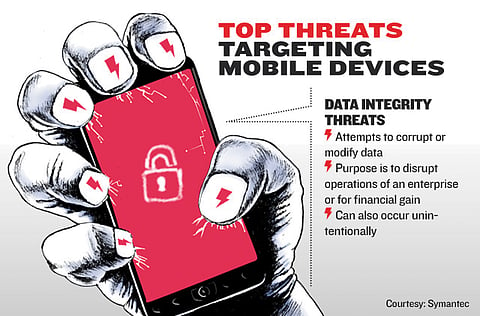
Data loss
Norton from Symantec says mobile devices face a number of threats today, with data loss being the biggest danger. Hackers use a number of ways to trick users into disclosing personal information; installing malware (viruses, worms and Trojans) on devices by replicating ‘social' applications; writing malware adapted for the mobile device, attempting to corrupt or modify data to disrupt operations for financial gain; sending spam from compromised devices, and web and network-based attacks launched by malicious websites or compromised legitimate sites which exploit the device's browser.
"Today's mobiles connect to an entire ecosystem of supporting services and the typical smartphone synchronises with at least one service that is outside the user's control. At the same time, many users also directly synchronise workplace mobile devices with home computers. In both scenarios, key assets may be stored in any number of insecure locations outside the direct view of the user and the business for which they work," said Tamim Taufiq, Head of Consumer Sales, MENA, Symantec.
Taufiq says increasing use of smartphones in the UAE and Saudi Arabia is partly responsible for the rising tide of malicious e-mails sent by global cybercriminals.
"Increased connectivity with the growing popularity of mobile devices is one factor behind the rising levels of spam in the Gulf. In the UAE, the mobile market is huge which makes it a huge market for cyber-criminals too.
"Cyber-criminals are also creating phishing sites - those designed to farm consumers' login details - specifically formatted for mobile phones," said Taufiq.
According to Symantec's 16th Internet Security Threat Report, mobile vulnerabilities increased by 42 per cent from 2009 to 2010. Downloaded apps (small bits of software to do everything from play games to search/track stocks) has also opened the floodgates for crooks seeking to maximise damage with one hit. Hackers slip in malicious codes through apps that are then downloaded across thousands of smartphones globally.
"While sneak attacks through "poisoned" apps and hidden malware may be obvious to the trained eye, new and unfamiliar users in particular are at high risk as cyber-criminals find new ways to replicate legitimate applications, leaving the victim's data wide open for the taking," says Taufiq.
Android under attack
Among smartphones, Android appears to be particularly vulnerable to attacks as it allows developers to post their apps directly, say security experts.
In March, over 58 apps on Android were found to contain malicious software that infected over 250,000 phones. Android remotely had to kill these apps and update the OS. Just recently yet another strain of malicious software, which logs and records calls and aimed at Android, was discovered. This comes close on the heels of a security hole discovered in Apple Inc.'s iPhones.
"Norton has already witnessed multiple attacks on Android. We've also seen attempts to evade Apple's strong security with criminals employing socially engineered attacks, such as phishing, to trick people into disclosing sensitive information," says Taufiq.
Tips to safeguard your cellphone
Consider mobile security software which can remotely lock, wipe or locate a lost device, and scans mobile apps to check if they are malicious
Always password-protect or screen lock your mobile device in case it is lost or stolen
Use common sense when accepting application permission requests to ensure they match the application features
Use a web filtering service (e.g. Norton DNS) when surfing the web
Courtesy: Norton from Symantec
Sign up for the Daily Briefing
Get the latest news and updates straight to your inbox


