Las Vegas: Some computers with wireless internet capabilities are vulnerable to attacks that could expose passwords, bank account details and other sensitive information even if the machines aren't actually online, researchers said.
The researchers demonstrated the vulnerability at a computer-security conference in Las Vegas, showing how to take complete control of a MacBook.
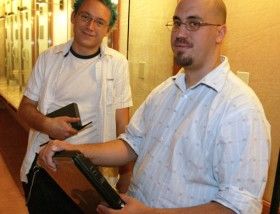
However, the two researchers, David Maynor, 28, and Jon Ellch, a 24-year-old who prefers to go by his hacker handle Johnny Cache, said the technique will work on an array of machines, including those that run Windows and Linux.
"The problem itself isn't really an Apple problem," said Maynor, a researcher at SecureWorks Inc, a network-monitoring company. "This is a systemic problem across the industry."
The technique, detailed during the first day of the Black Hat conference, has broad implications for the large number of people who over the past five years have grown accustomed to connecting to the internet wirelessly while sitting in airports, hotels and cafes.
"It's alarming," said Phil Zimmermann, a software engineer who specialises in data security. "Now I would rather connect using a cable," he said.
Maynor and Cache showed a video in which they dropped what is known as a 'root kit' into a MacBook by exploiting a weakness found in a wireless card, a component that uses radio waves to connect to the internet.
A root kit is a virtually undetectable program that criminals can use to do things such as log passwords and access sensitive files. Maynor was able to create, read and delete files on the Apple laptop.
The MacBook used in the demonstration was not using the wireless gear that was shipped with the computer.
Instead, they used a third-party wireless card. Apple spokeswoman Lynn Fox declined to comment.
Maynor said the flaws are so common that he'd have no trouble walking into an internet cafe and finding someone vulnerable.
He said the technique could be useful in targeting specific people or specific groups who are in close proximity to an attacker for instance, a cafe that is frequented by executives of a particular company.