Hidden bug in FPGA chips can help hackers steal critical data
A critical vulnerability in FPGA chips can help hackers steal key data of enterprises
London: A team of German researchers has discovered a critical vulnerability in FPGA chips, part of Cloud data centres, mobile phone base stations, encrypted USBs and industrial control systems, that can help hackers gain complete control over chips and steal key data of governments and enterprises.
Field Programmable Gate Arrays, FPGAs for short, are flexibly programmable computer chips that are considered very secure components in many applications.
In a joint research project, scientists from the Horst Gortz Institute for IT Security at Ruhr-Universitat Bochum and from Max Planck Institute for Security and Privacy in Germany discovered that a critical vulnerability is hidden in these chips.
They called the security bug "Starbleed". Since the bug is integrated into the hardware, the security risk can only be removed by replacing the chips. The manufacturer of the FPGAs has been informed by the researchers.
With these programmable chips, a user can write software that loads onto a chip and executes functions.
The advantage of FPGA chips lies in their reprogrammability compared to conventional hardware chips with their fixed functionalities.
This reprogrammability is possible because the basic components of FPGAs and their interconnections can be freely programmed.
In contrast, conventional computer chips are hard-wired and, therefore, dedicated to a single purpose.
The linchpin of FPGAs is the 'bitstream', a file that is used to programme the FPGA.
In order to protect it adequately against attacks, the bitstream is secured by encryption methods.
Dr Amir Moradi and Maik Ender, in cooperation with Professor Christof Paar succeeded in decrypting this protected bitstream, gaining access to the file content and modifying it.
To overcome the encryption, the research team took advantage of the central property of the FPGAs: the possibility of reprogramming. The scientists were able to manipulate the encrypted bitstream during the configuration process.
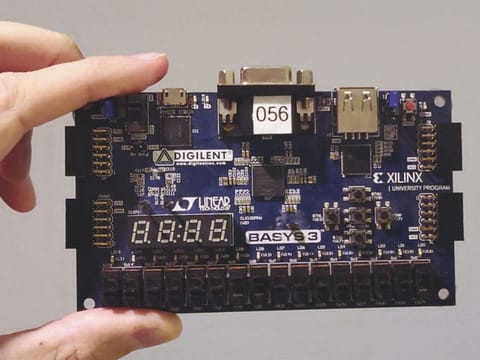
As part of their research, the scientists analysed FPGAs from Xilinx, one of the two market leaders in field-programmable gate arrays.
The 'Starbleed' vulnerability affects Xilinx's 7-series FPGAs with the four FPGA families Spartan, Artix, Kintex and Virtex as well as the previous version Virtex-6, which form a large part of Xilinx FPGAs used today.
"We informed Xilinx about this vulnerability and subsequently worked closely together during the vulnerability disclosure process. Furthermore, it appears highly unlikely that this vulnerability will occur in the manufacturer's latest series," explained Moradi.
"If an attacker gains access to the bitstream, he also gains complete control over the FPGA. Intellectual properties included in the bitstream can be stolen. It is also possible to insert hardware Trojans into the FPGA by manipulating the bitstream," warned Paar.
Since the security gap is located in the hardware itself, it can only be closed by replacing the chip.
"Although detailed knowledge is required, an attack can eventually be carried out remotely, the attacker does not even have to have physical access to the FPGA," Paar added.
The security researchers are set to present the results at the 29th Usenix Security Symposium, scheduled to be held in August in Boston, Massachusetts.


